When it comes to protecting patient data, following breach prevention best practices is non-negotiable. Robust security measures are necessary during medical record handling. This principle is especially true with the popularity of digital healthcare information.
The consequences of a data breach in the healthcare sector are far-reaching and severe. Patients’ privacy is in danger, and data breaches can result in identity theft and financial fraud.
Breach prevention must be an ongoing commitment to address these risks. It requires continuous monitoring, evaluation, and adaptation to address emerging threats and evolving regulations.
Protect your medical records with ChartRequest.
Why Do Data Breaches Happen?
The answer may seem obvious, but most data breach attacks against healthcare practices have financial motivations.
Medical record thieves threaten patient privacy by selling medical records to criminals and committing identity fraud.
Data breaches are on the rise due to human and technical vulnerabilities. Here are some key factors that contribute to data breaches:
- Weak Security Measures: Simple passwords, lack of encryption, or outdated software create risks for attackers.
- Social Engineering: Attackers manipulate human emotions through social engineering techniques like phishing. The goal is to trick people into sharing access to sensitive data.
- Insider Threats: Malicious insiders might have authorized access to sensitive data. They may intentionally leak or misuse the information for personal gain or to harm the organization.
- Third-Party Risks: Organizations often collaborate with external vendors or business partners. Third parties can mishandle protected data, risking severe breaches.
- Advanced Persistent Threats: Sophisticated cybercriminals use advanced techniques to gain unauthorized access to systems. These attacks often remain undetected for extended periods, allowing them to extract terabytes of sensitive data.
Now that you know why and how data breaches happen, let’s cover breach prevention best practices.
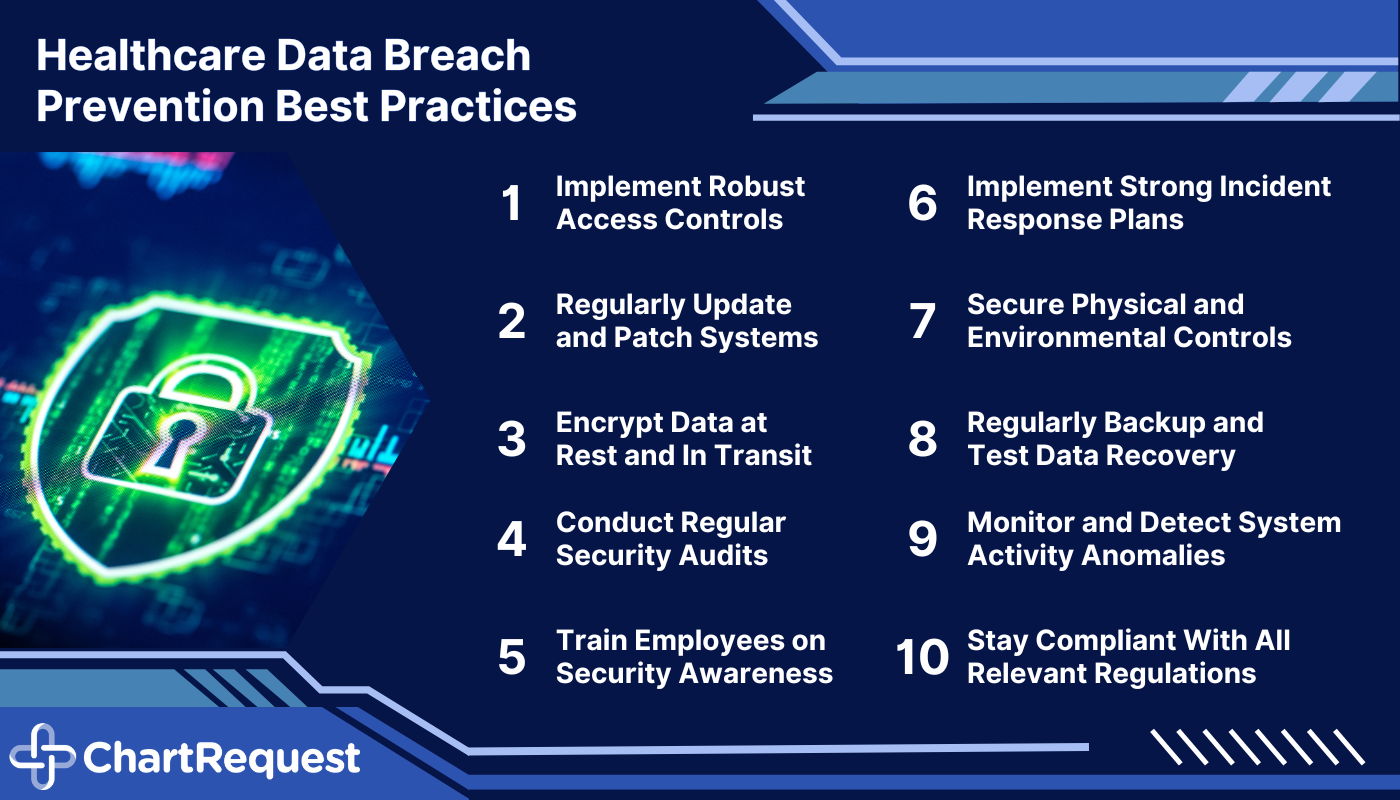
1. Implement Robust Access Controls
Implementing access controls plays an essential role in data security. Only authorized individuals should have access to sensitive information. By using encryption methods like SSL, your organization can reduce the risk of data breaches.
Establishing strong passwords is the first line of defense against data breaches. It is vital to enforce password policies with guidelines on length, complexity, and uniqueness. To add an extra layer of security, it’s helpful to use password management tools and multi-factor authentication (MFA).
Role-based access control (RBAC) safeguards data based on users’ roles and responsibilities within the organization. It also allows administrators to assign specific permissions and privileges to individuals. These users can only access the information necessary for their job function.
2. Update and Patch Systems
Routine updates and patches are an IT-recommended breach prevention best practice. These responsibilities address vulnerabilities and reduce the risk of runaway network infiltration.
Integral aspects of patch management include keeping software and systems up-to-date. Depending on your system, the latest security enhancements and bug fixes can fortify your EHR against numerous threats.
It’s imperative to conduct vulnerability assessments throughout the year. Staying updated on security bulletins and software updates can help reduce the risk of breaches.
3. Encrypt Data in Transit and at Rest
Encryption protects patient data, both during transmission and storage. This best practice strengthens breach protection by scrambling sensitive data in a way that requires a particular “key” to revert.
Encrypting sensitive information ensures that — even if intercepted or accessed by unauthorized individuals — the data remains unusable.
Encrypting data in transit involves securing information during transmission. You can use protocols like HTTPS or VPNs to accomplish this goal.
Encrypting data at rest refers to securing information stored in databases and using encryption to transform the data into an unreadable format. For example, if someone managed to hack into the database, they wouldn’t be able to read any of the data.
4. Conduct Regular Security Audits and Assessments
Regular security audits and assessments are essential breach prevention best practices for protecting patient data. These reviews help detect and address potential security weaknesses across the digital infrastructure.
Here are a few key points to consider regarding conducting regular security audits and assessments:
- Identifying Vulnerabilities: Periodic security audits help identify vulnerabilities in healthcare systems, processes, and infrastructure. Review network configurations, access controls, encryption protocols, and physical security measures.
- Compliance With Regulations: Review privacy policies, data handling procedures, and incident response plans to ensure compliance with HIPAA.
- Detecting Emerging Threats: Regular assessments enable organizations to stay ahead of emerging threats. Staying informed about cybersecurity trends, threat intelligence, and industry-specific vulnerabilities can help you address risks before they become issues.
5. Train Employees on Security Awareness
You should be able to trust your employees to defend against potential threats. Their knowledge and adherence to security best practices can strengthen data breach prevention.
Employees are responsible for protecting sensitive patient data during transfers and use. When they understand their role in breach prevention, they can be a convenient safeguard against cybercriminals.
Still, security risks and criminal techniques will continue to evolve. Employees must receive ongoing training and awareness programs to recognize and respond to attempted attacks. Security awareness training for data breach prevention should cover various topics, including:
- Password best practices
- Common cyberattack strategies
- Secure data handling and disposal
- Incident reporting procedures
- The importance of physical security measures
- Possible consequences of data breaches
6. Implement Strong Incident Response Plans
A well-defined incident response plan may not prevent a direct breach, but these best practices enable your team to handle security incidents more effectively.
Key points to consider when developing an incident response plan include:
- Outlining responsibilities, communication protocols, and steps for recovering from security incidents
- Prioritizing prompt response to minimize the impact of breaches
- Conducting a thorough investigation when a security incident occurs. Analyze evidence, identify the root cause, and assess any impact on patient data and privacy.
- Focusing on containment and recovery after a breach.
Communicate with your team and follow Breach Notification Rule regulations to maintain transparency.
7. Secure Physical and Environmental Controls
Healthcare organizations must implement other measures to safeguard their physical infrastructure and create a secure environment for sensitive information. The HIPAA Security Rule should be a baseline for its physical, technical, and administrative protections.

Physical security measures also protect against unauthorized access, theft, and tampering with patient data. Restricting physical access to data areas can minimize the risk of breaches and unauthorized data handling.
Physical security reviews and assessments are necessary. Audits help identify any weaknesses or vulnerabilities in security measures. Conducting periodic inspections, reviewing access logs, and testing alarm systems are essential components of physical security audits.
8. Backup and Test Data Recovery
Backing up data and testing recovery procedures is a critical best practice in breach prevention. Data backup ensures that you can restore your systems and resume normal operations after a ransomware attack, system failure, or other natural disaster.
Healthcare organizations should establish a regular data backup schedule that minimizes the risk of data loss. To enhance data protection, you should implement a redundant backup system to mitigate the risk of data loss.
Clear and well-documented data recovery procedures with step-by-step instructions help prevent mistakes during a critical time.
9. Monitor and Detect Anomalies in System Activity
Breach prevention best practices include monitoring and detecting anomalies in your data system. This due diligence identifies possible threats and unauthorized access attempts.
Deploy tools to monitor network traffic, log files, user activity, and system behaviors in real-time. It’s wise to put automated alerting mechanisms in place to notify security teams of detected anomalies or potential security incidents. Prompt notifications enable security teams to investigate and respond to incidents on time.
Regular log analysis can help you uncover indicators of compromise and provide valuable insights for recovery investigations.
10. Stay Current With Regulatory Compliance
You and your team must have a thorough understanding of relevant data protection regulations. There is no shortage of regulations designed to protect patient privacy and ensure quick access to medical records.
Here are key points to consider:
- Get familiar with medical data regulations, such as HIPAA. The Health Insurance Portability and Accountability Act of 1996 requires secure handling, storage, and transmission of patient data.
- Understand the penalties for non-compliance. Violations can result in severe consequences, including financial penalties, reputational damage, and loss of patient trust.
- Assess your compliance protocols on a routine basis. This method involves conducting internal audits, reviewing policies and procedures, and ensuring necessary safeguards and controls are in place.
- Collaborate with compliance professionals who specialize in data protection regulations. They can provide guidance, conduct audits, and offer expertise to ensure you remain compliant with changing regulatory requirements.
Strengthen Your Data Breach Prevention Best Practices
Following breach prevention best practices is crucial for your organization.
By partnering with ChartRequest, you can rest assured that your patient data is safe. Our dedicated team works tirelessly to maintain the highest level of HIPAA security and compliance.
Ready to learn more about how ChartRequest helps protect patient data?
Set up a consultation with our record experts today.


